From Darwinism in IT Security, Pt. 3: Time to Deal with These No-Good Parasites:
[Detection] adoption has become the norm in the IT-security industry; and based on that, a whole ecosystem of parasites now successfully bullshits (successfully – i.e., keeps getting away with it!) the public. No, I am not making this up.
What all parasites agree on is their opposition to ‘traditional methods’ (the very same scanning methods they adopt via VirusTotal) and their love of all things ‘next generation’ (though what exactly is new about detection copy-and-pasting – and also AI – they don’t point out).
Conclusion: if you get approached by folks from an unknown company bandying about words like ‘next-gen’, ‘behavioral analysis’, ‘artificial intelligence’, etc., with no results of independent tests to make those words mean something real, watch out. The marketing materials of such companies show that the only artificial intelligence they use is that for peaking on real IT-security companies via the cloud.
It’s like I said before, you have to wonder about security vendors who do not willingly submit themselves to third party scrutiny. If their products are as good as their marketing claims, this will prove itself out in third party testing, or better yet, your own testing using objective criteria. Reputable security vendors are more than willing to support such an effort.
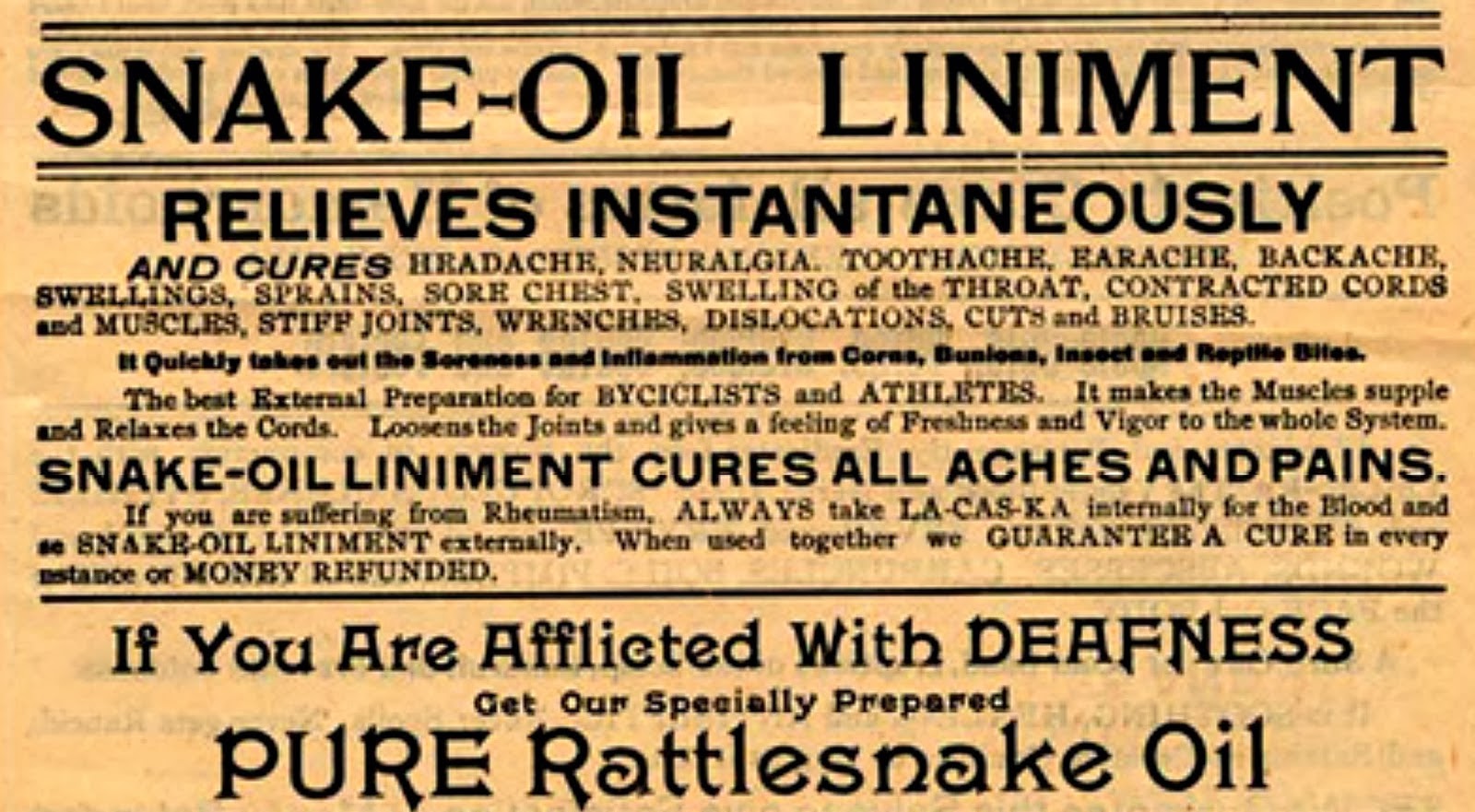
If you rely purely on marketing to make decisions about what security solutions to buy, you may be buying snake oil. Caveat emptor!