This past week, I've been on the Check Point Security Tour up in Western Canada talking about the Dangers of Social Networking. The basis of the presentation was actually something I gave to Check Point employees in Redwood City back in August on the benefits of social networking. I added the "dangers" part after I was asked to present in this tour :)
This topic seem quite timely as this past week, several of my followers on Twitter got bit by the latest attempt at hacking Twitter accounts. At least three of my followers sent me direct messages on Twitter that were a little suspicious:
this youz ? ? http://is.gd/4H1qh
lost a ton of weight and feel better here http://ringys4u.com
hi. i lost excess fat with http://loseweight.asdjiiw.com it works...
These message looked suspicious. I didn't click on the links and I immediately warned the affected individuals to change their passwords.
Of course, Twitter is not the only place this happens. In fact, these kinds of messages have being sent out as long as email spam has been around, which have been going on at least as long as I've been on the Internet.
Nothing New Under The Sun
I've been at this "social networking" thing a while. Aside from starting out on computer bulletin boards in the late 1980s (you know, the kind you used your computer modem to dial into), which is one of the earlier forms of so-called social networking, I've participated in IRC, instant messaging, USENET, mailing lists (also ran my own for 9 years), online forums, blogging (phoneboy.com has been one since 2005), and of course use the "current" social networking tools like Twitter and Facebook.
The main thing that differentiates these service from one another is the interface used and whether or not the services permitted real-time communication with others. Beyond that, they all fulfill a fundamental human need--the need to be heard and understood by others.
The Value of Social Networking
By this point in time, I think most of us understand why social networking is valuable. It's great for making new connections with people, strengthening existing connections with people, being part of (or starting) a conversation, and sharing ideas and things you've created.
For business, it can even be more powerful. Connecting with more customers more often can mean more sales. It can also allow you to get better visibility into what's going wrong with your business, for example customer service snafus. Businesses have to accept that they cannot control the conversation about them. However, they have a fighting chance of guiding it in the right direction by actively participating in the conversation.
Where Email and "Social Media" Tools Differ
It's relatively easy to send an unsolicited email to someone. All you have to do is find their email--or guess it--and send them an email. Furthermore, it's relatively easy to "spoof" an email. I figured out in the early 1990s how to send an email from someone appearing to be from "root@heaven.org" by talking directly with the email server. While mail servers have gotten smarter about these things over the years, it can still be done relatively trivially.
The newer social media tools make this a bit more challenging as a "friend" or "follower" relationship is required. For example, I can only send someone a direct message on Twitter to someone that is actually following me. Facebook requires the person to be a "friend." This severely limits who can send you a private message and you can be fairly certain who sent the message to you.
Despite these controls, I still see "spam" on Twitter and Facebook. And yes, like what happens with email from time to time, it appears to come from a "friend." But unlike email, where your identity can be easily spoofed, something more nefarious has to happen.
URL Shorteners
Prior to Twitter, there was not a huge called for so called URL Shortening services, which take a long URL and make it shorter. tinyurl.com is one of the oldest such services. However, the limited message size of Twitter and the increase in URLs shared over the service necessitated the use of these services in order to allow for text to accompany the URL and, of course, allow for URLs that might be longer than 140 characters :)
URL Shorteners are great for exactly this reason--they make long URLs shorter. They also provide other services as well, such as the ability to see who clicked on the link and when. However, they are also bad because they mask the original URL, which, if you could see it, might cause you not to click on that link. For example, would you click on a link for either of these URLs?
- http://www.xzxxy.cn/cgi-bin/pwn-system?type=win
- http://www.paypal.com.hax0r.pl/webscr?cmd=_home
You can tell by looking at these URLs that something is up. However, Look at these two URLs:
- http://bit.ly/3Ha5Mo
- http://bit.ly/N03v1l
Can you tell what evil might lurk behind these shortened links just by looking at the link?
How Do I Get Spam From My Friends on Social Networking Sites?
With friends sending you benign looking links via direct message, we have ourselves a perfect storm for the spreading of spam. Theoretically, these messages came from someone you trust, causing you to let down your guard and think it's ok to click on the link. The link leads to a website that contains a piece of malware that, without your knowledge or consent, either steals your Twitter credentials stored on your computer, or hijacks your existing Twitter session and sends out similar links to your friends. Or much worse.
While that can and does happen, the other possibility is that you were flat out tricked into giving your Twitter credentials to a third-party that either looked like the Twitter site or purported to do something of benefit to you (e.g. help you gain more followers). While not all third-party sites that ask for your Twitter credentials are bad, some are.
Information Disclosure
Speaking of information disclosure, there are plenty of other opportunities to disclose information on social networking sites that, under a different context, you might not disclose. My buddy Kellman has a great post on those "quizzes" that make the rounds from time to time and what great sources of information they can be about you. While some of the questions are truly innocuous, some "key" questions could be sprinkled in there that, when used in the right circumstances, could easily be used to "reset" an account password or gain access to an account.
Protect Yourself
The dangers in social networking aren't new at all. They've been there for at least a decade. Fortunately, the ways to protect yourself aren't new, either, though far too many people forget the basics.
Careful With That Link, Eugene: Like links you receive in email, particularly unsolicited ones, all links on social networking sites should be carefully evaluated. Since the links themselves are often shortened URLs, look at then text around it. Usually that text is a huge clue as it contains misspelling or contains "spammy" looking text. Your account could be sending those same kinds of messages if you're not careful about what links you click on.
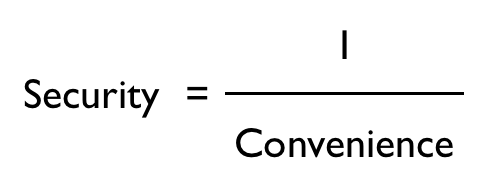
Use Different Passwords, Change Them Often: Each of your social networking sites as well as all other important websites should have different, complex password assigned to them, and they should be changed regularly. Since people often use the same password on multiple sites, one compromised account could easily lead to compromising other accounts.
Don't Blindly Give Out Your Credentials: There are a lot of third party web-based services out there that make use of your social networking services. In the past, the only way for this to occur was to give your credentials to these services. This works, so long as these third party services weren't somehow compromised, or worse, the services were not what they seemed to be. The one benefit to using something like OAuth (which Twitter does) is that you can revoke a web applications permission quite easily. It doesn't prevent the third party web service from being compromised.
Keep Your Operating System, Browser Patched: Ensure you have applied all the latest patches from Microsoft, Apple, or whomever supplies your computer's underlying operating system. Ensure you are using the latest version of your web browser. If you are using Internet Explorer--especially if you are using Internet Explorer version 6, as is standard on Windows XP, try using a third party browser such as Firefox or Google Chrome.
Browser Plugins Can Help: If you are using Firefox, there are plugins that can help expand those "short" URLs so you can see where it is they will take you. LongURL is a good example of this for Firefox.
Security Software: Windows users should ensure they are running an up-to-date set of security tools that cover anti-virus, anti-malware, and protection from browser-based attacks. Microsoft puts out a free anti-virus/anti-malware tool which is quite good, as does a few other companies. Their free tools do not protect against browser-based attacks. Something like ZoneAlarm ForceField or ZoneAlarm Extreme Security (which includes ForceField and other security features) can be effective protection against these kinds of tools. (Disclosure: I work for Check Point Software, which publishes ZoneAlarm).
Nothing Is Completely Private: Even if you protect your updates on Twitter or are very careful about whom you interact with on Facebook, note that all communications, even so-called "direct" or "private" messages, are not entirely private on social networking services. Accidental disclosure can and does happen, thanks to actions by you or your so-called friends. It's not always intentional, of course, but it does happen. And yes, those "quizzes" you might take may contain a so-called identity question that could be used to take over one of your other accounts. Just be careful.
Some Final Thoughts
Social networking has been, and continues to be, quite pervasive in the civilized world. The tools used for this have and will continue to change over time. What hasn't changed is that there are people out there who do not have your best interest at heart. And while nothing is entirely safe and secure, with a little vigilance, we can spend less time being victims of the latest scam and more time doing what we're supposed to do on these social networks: communicating and sharing.