As I’m sure you’ve heard by now, Cloudflare had a case of CloudBleed, causing what amounts to a massive privacy violation for any site that happened to use them, at least if they used one of three specific features of Cloudflare: Email Obfuscation, Server-side Excludes, and Automatic HTTPS Rewrites. A potential list of compromised sites showed up, which may not be entirely accurate because plenty of sites use Cloudflare but may not necessarily use these features.
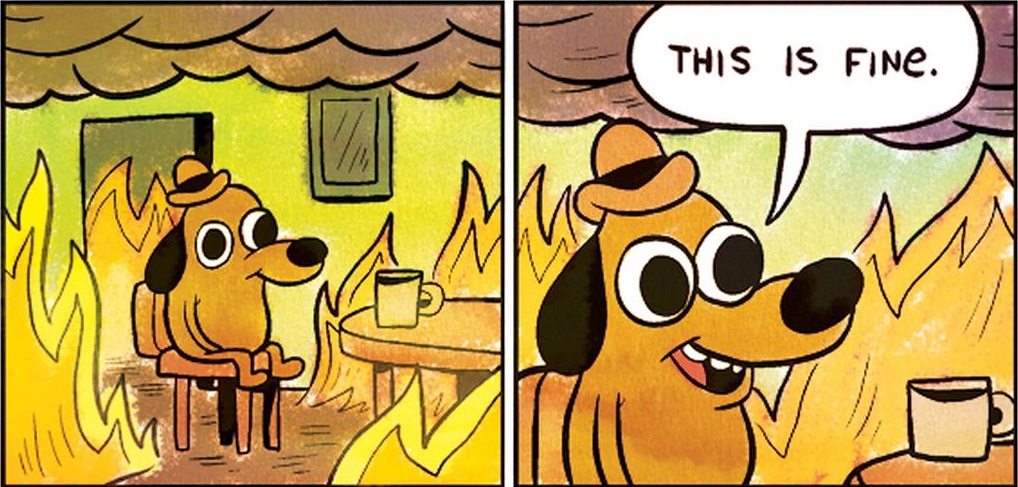
The advice that is given as a result of this bug?
Check your password managers and change all your passwords, especially those on these affected sites. Rotate API keys & secrets, and confirm you have 2-FA set up for important accounts. This might sound like fear-mongering, but the scope of this leak is truly massive, and due to the fact that all Cloudflare proxy customers were vulnerable to having data leaked, it’s better to be safe than sorry.
Theoretically sites not in this list can also be affected (because an affected site could have made an API request to a non-affected one), you should probably change all your important passwords.
Which is fine if, like me, you actually use a password manager (I recommend LastPass). However, it’s not entirely complete advice as “HTTP cookies, authentication tokens, HTTP POST bodies, and other sensitive data” were leaked. Changing passwords won’t suddenly fix this disclosure issue, particularly if the sites in question do a poor job invalidating cookies and tokens. Think that’s far fetched? Think again.
Changing passwords also doesn’t fix applications that may have communicated on the backend to a Cloudflare-backed site (either on your behalf or otherwise). The potential scope of this issue is…scary.
That said, I can’t imagine every one who ever used a given service over the last several months had their information disclosed. While this event increases the risk above zero, it’s not clear by how much for a given user. Also, the impact of disclosure of a login cookie/token for my bank or a service like Cloudflare is far different than for a site like Techdirt, which out of an abundance of caution is forcing everyone to reset their password on the site.
I feel sorry for the average Internet user, who has seen umpteen of these notifications lately (just from Yahoo alone)! The advice of “change all your passwords” is quite simply untenable for the vast majority of Internet users. Even though I use a password manager as part of good password hygiene, I certainly don’t have time to visit all the sites in LastPass, much less change all my passwords manually!
And, as I noted earlier, changing your password won’t fully address the issue. Still, it’s probably as a good a time as any to make sure your critical accounts are as protected as they can be. For me, that meant changing my Cloudflare password and API key as well as enabling multi-factor authentication. I’ve also changed the password for a few sites listed on the potential list of compromised sites. I will keep checking LastPass in case they decide to integrate this list of sites into their Security Challenge, which they’ve done in the past.
Even if you do none of this, my guess is that the vast majority of the users won’t be impacted by CloudBleed. At least I hope they won’t be.
Disclaimer: My employer, Check Point Software Technologies, didn’t offer an opinion on this issue. The above thoughts are my own.